Cybersecurity Trends – BEC Phishing
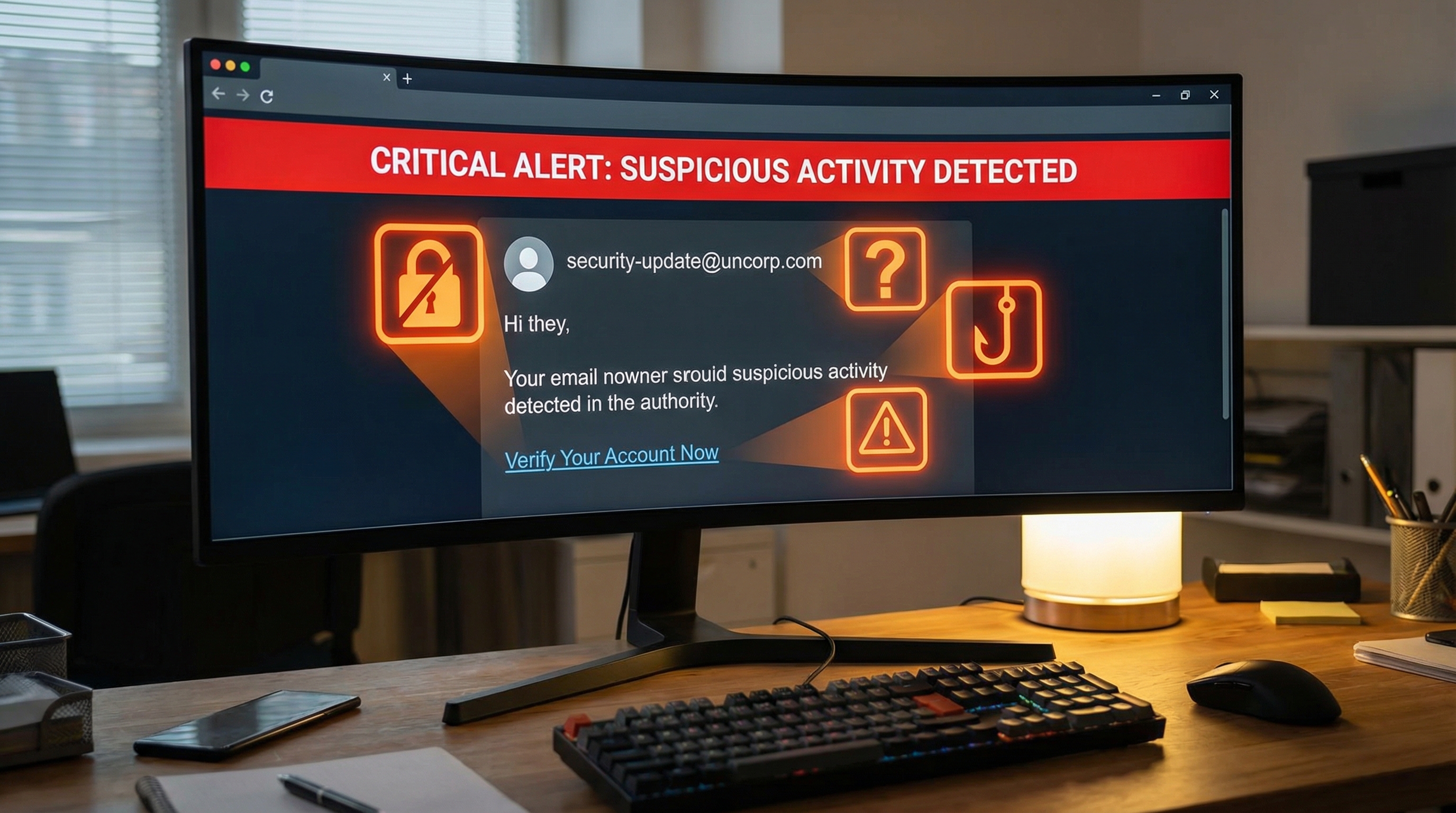
Business Email Compromise (BEC) has emerged as one of the most financially damaging forms of cybercrime. Unlike traditional phishing that casts a wide net, BEC attacks are highly targeted, well-researched, and devastatingly effective.
What is BEC?
BEC attacks involve criminals impersonating executives, vendors, or other trusted parties to trick employees into transferring funds or revealing sensitive information. Common scenarios include:
- CEO Fraud: Attacker poses as the CEO requesting an urgent wire transfer
- Vendor Impersonation: Attacker poses as a supplier requesting payment to a new bank account
- Account Compromise: Attacker gains access to a legitimate email account and uses it to make fraudulent requests
- Attorney Impersonation: Attacker poses as legal counsel handling a confidential matter
Why BEC is So Effective
BEC attacks succeed because they:
- Don't rely on malware that security software might detect
- Exploit human trust and authority relationships
- Often involve careful research about the target organization
- Create urgency that bypasses normal verification procedures
- Request actions that employees are authorized to take
The Financial Impact
According to the FBI, BEC attacks have caused over $50 billion in losses globally. Individual incidents often involve six or seven-figure losses. And unlike credit card fraud, wire transfers are difficult to reverse once completed.
Protecting Your Organization
Defense against BEC requires multiple layers:
- Email Security: Implement email authentication (SPF, DKIM, DMARC) and advanced threat protection
- Process Controls: Require multi-person approval for large transfers; verify requests through a separate channel
- Employee Training: Teach employees to recognize BEC red flags and verify unusual requests
- Vendor Management: Verify any changes to vendor payment information through established contacts
- Culture: Create an environment where employees feel comfortable questioning suspicious requests, even from executives
Red Flags to Watch For
- Requests for urgency or secrecy
- Requests that bypass normal procedures
- Changes to payment information
- Unusual timing (holidays, end of day)
- Slight variations in email addresses
- Pressure not to verify through other channels
Response Planning
Include BEC scenarios in your incident response planning. Know how to quickly contact your bank to attempt recovery of fraudulent transfers, and have clear escalation paths when suspicious requests are identified.